Security Hardening
SecHard provides automated security hardening auditing, scoring and remediation for servers, clients, network devices, applications, databases, and more.
Centralized Device Management and Performance Monitoring
IT environments requires complete visibility into both device configurations and system performance.
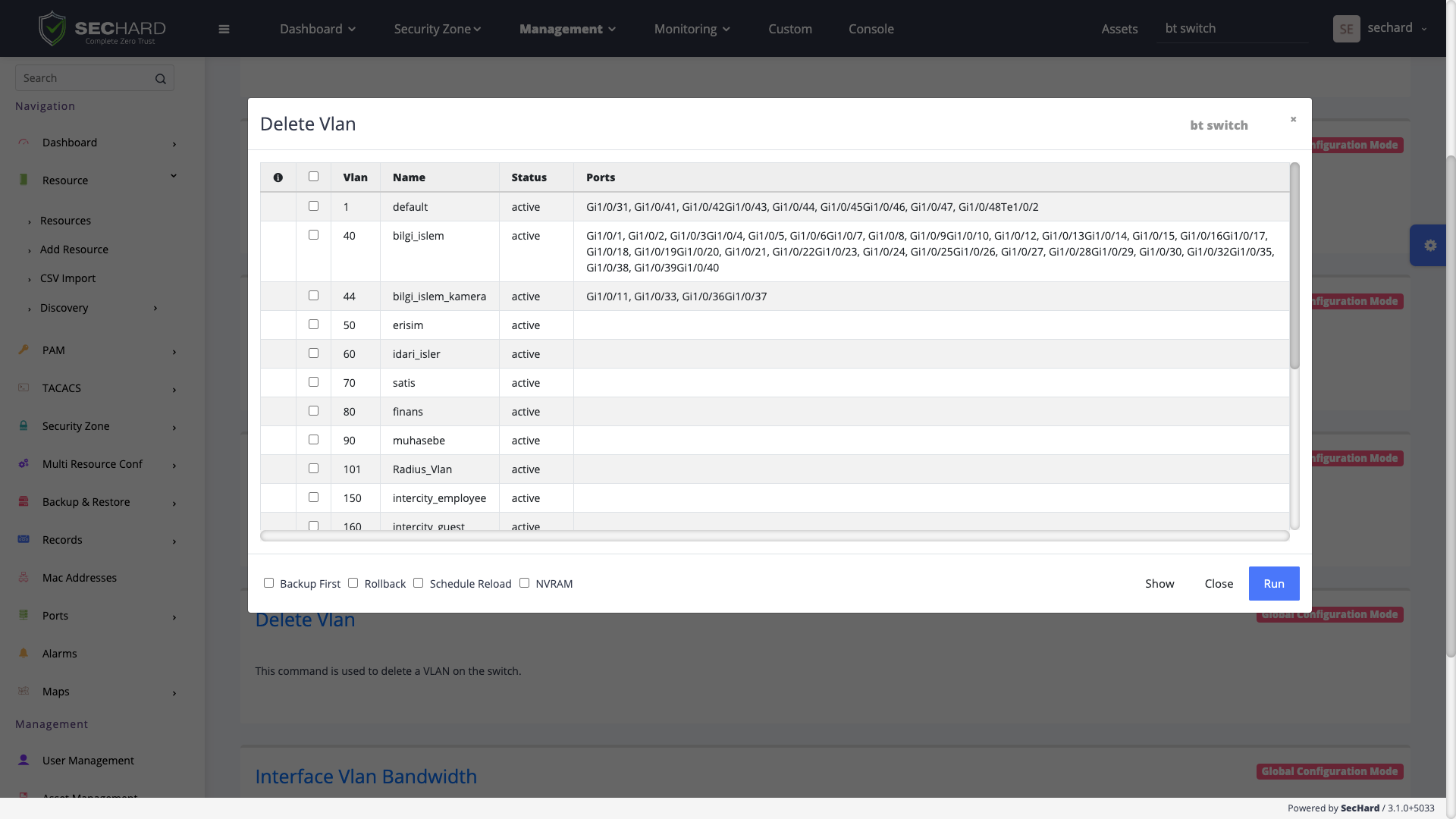
SecHard Device and Performance Manager provides a unified platform that enables organizations to manage network devices,
monitor infrastructure performance, and maintain operational stability from a single interface.
The solution combines network device management, configuration control, and performance monitoring capabilities to help IT
and security teams efficiently manage their infrastructure. With real-time monitoring, automated configuration management, and centralized control,
organizations can reduce operational complexity while improving system reliability and security.
By maintaining centralized visibility over device configurations, organizations can ensure consistent network policies
and quickly recover from configuration failures or system outages.
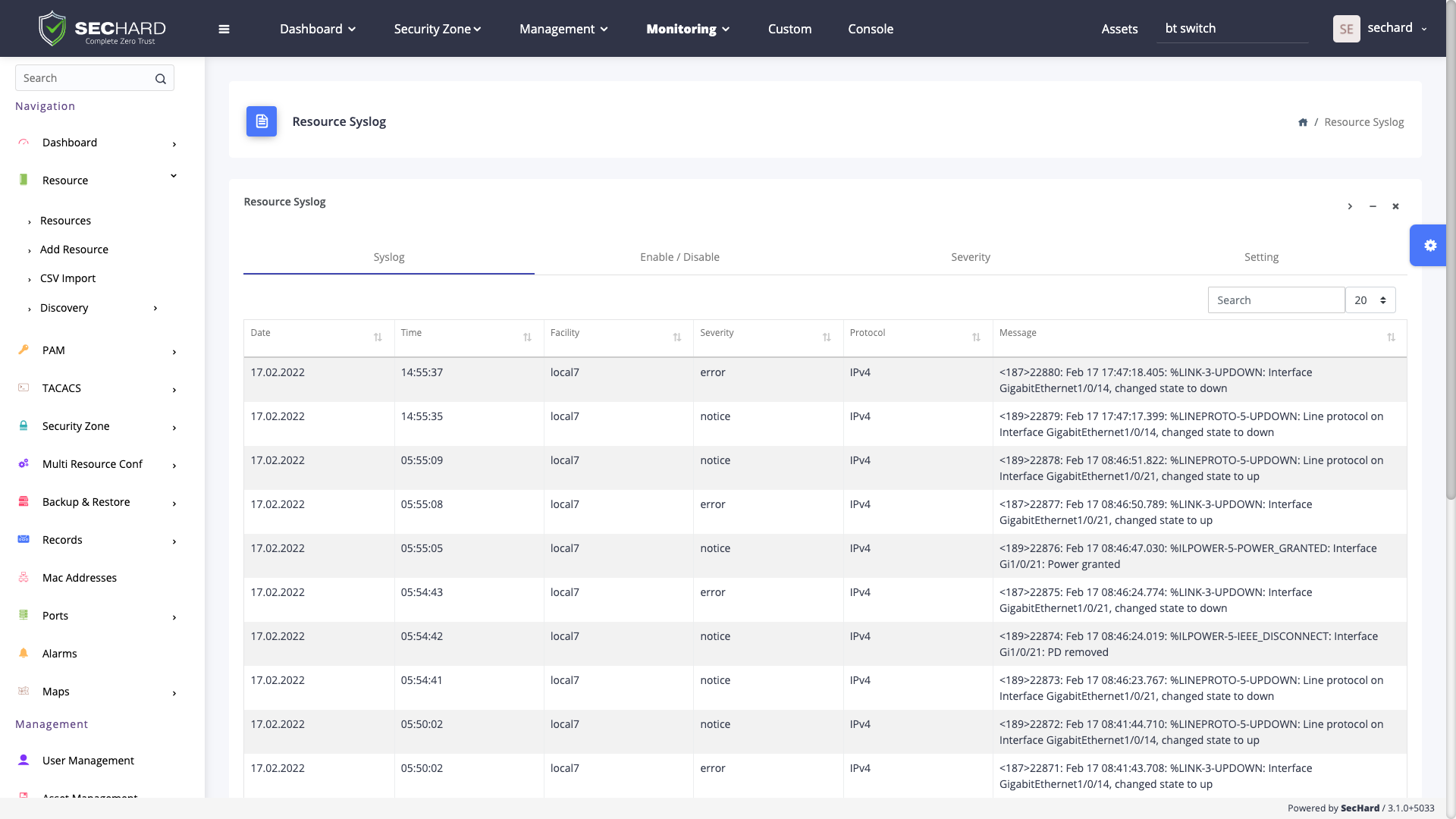
Real-Time Alerts and Infrastructure Visibility
SecHard continuously analyzes device activity and performance metrics to detect anomalies or critical events in real time.
When predefined thresholds are exceeded or abnormal behavior is detected, the platform generates instant alerts that enable IT teams to take proactive action.
These alerts help prevent downtime, improve response times, and maintain system availability.
By combining performance monitoring, device management, and real-time alerting, SecHard provides organizations with complete visibility into their IT infrastructure.
SecHard provides automated security hardening auditing, scoring and remediation for servers, clients, network devices, applications, databases, and more.
A powerful identity and access management software to get compliant with Cyber Hygiene and to prevent attacks like privilege abuse, ransomware and more!
SecHard solves the risk awareness problem in asset management. Automated discovery, access, identify and remediation features provide ultra-wide visibility for all regulations.
With the passive scanning method, SecHard operates the vulnerability detection and management processes for all IT assets without creating any risks.
SecHard auto-discovers the certificates in companies’ environment, reports the expiration dates of these certificates, and it can automatically renew some of these certificates through well-known certificate authorities.
SecHard's unique risk assessment formula calculates the real-world risk scores by combining asset group risk scores, security hardening scores, and vulnerability scores.
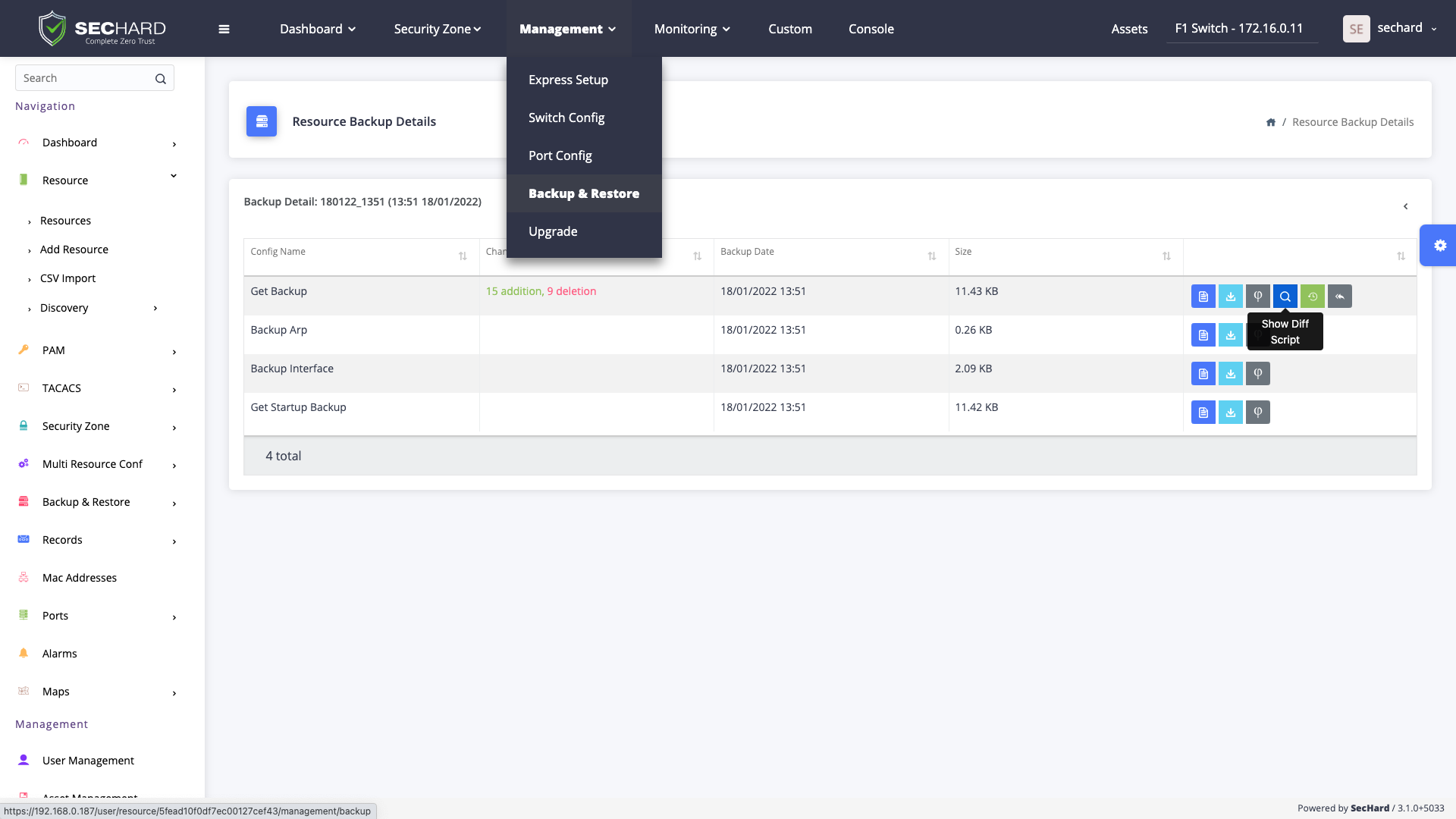
Powerful and customizable network device management with backup/restore, configuration change detection, performance monitoring, bandwidth monitoring, and firmware upgrade.
Powerful and customizable network device management with backup/restore, configuration change detection, performance monitoring, bandwidth monitoring, and firmware upgrade.
Centralized Authentication, Authorization and Accounting (AAA) for *nix systems and network devices with Microsoft Active Directory integration.
Book a meeting with SecHard experts.
