Security Hardening
SecHard provides automated security hardening auditing, scoring and remediation for servers, clients, network devices, applications, databases, and more.
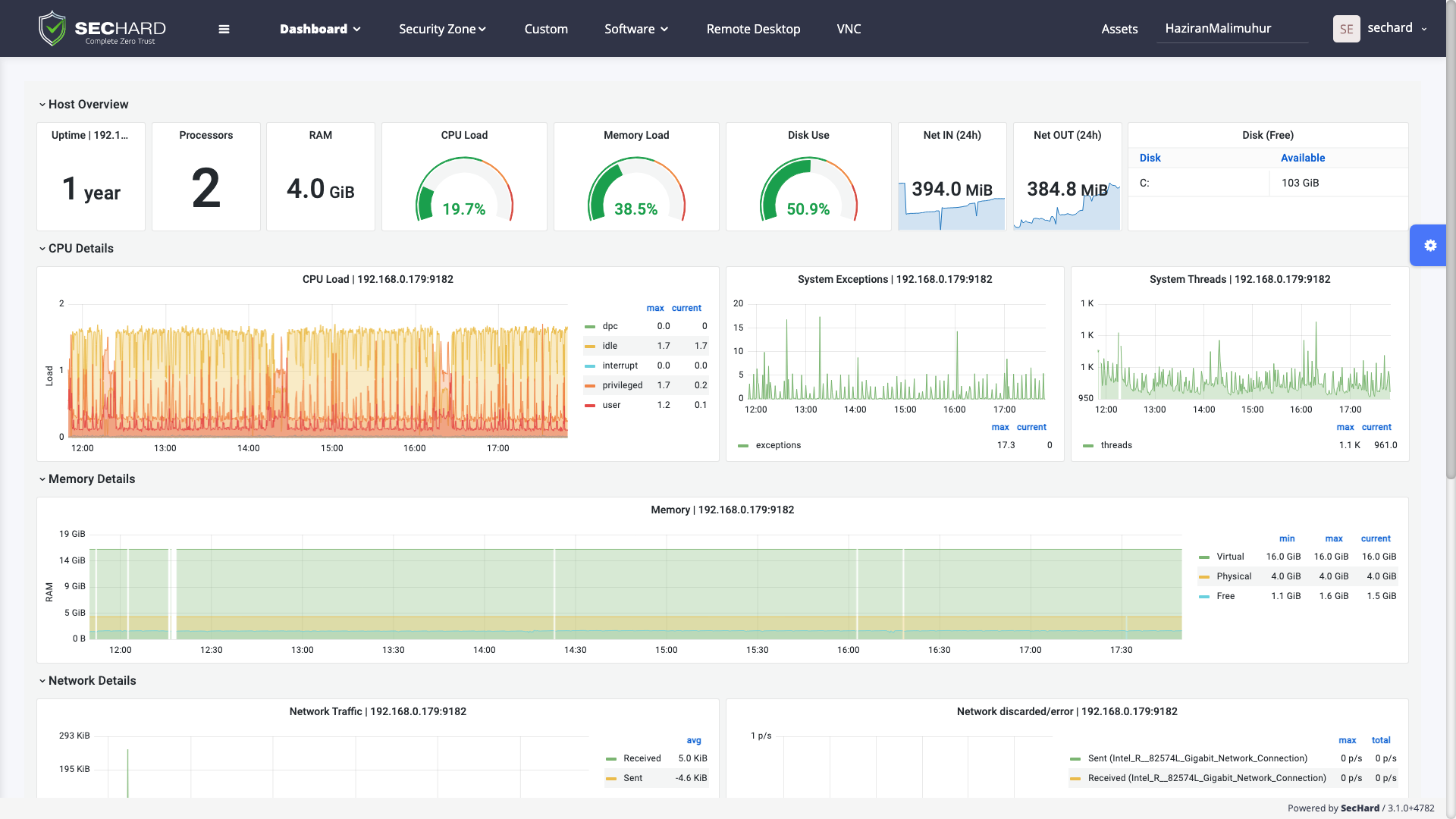
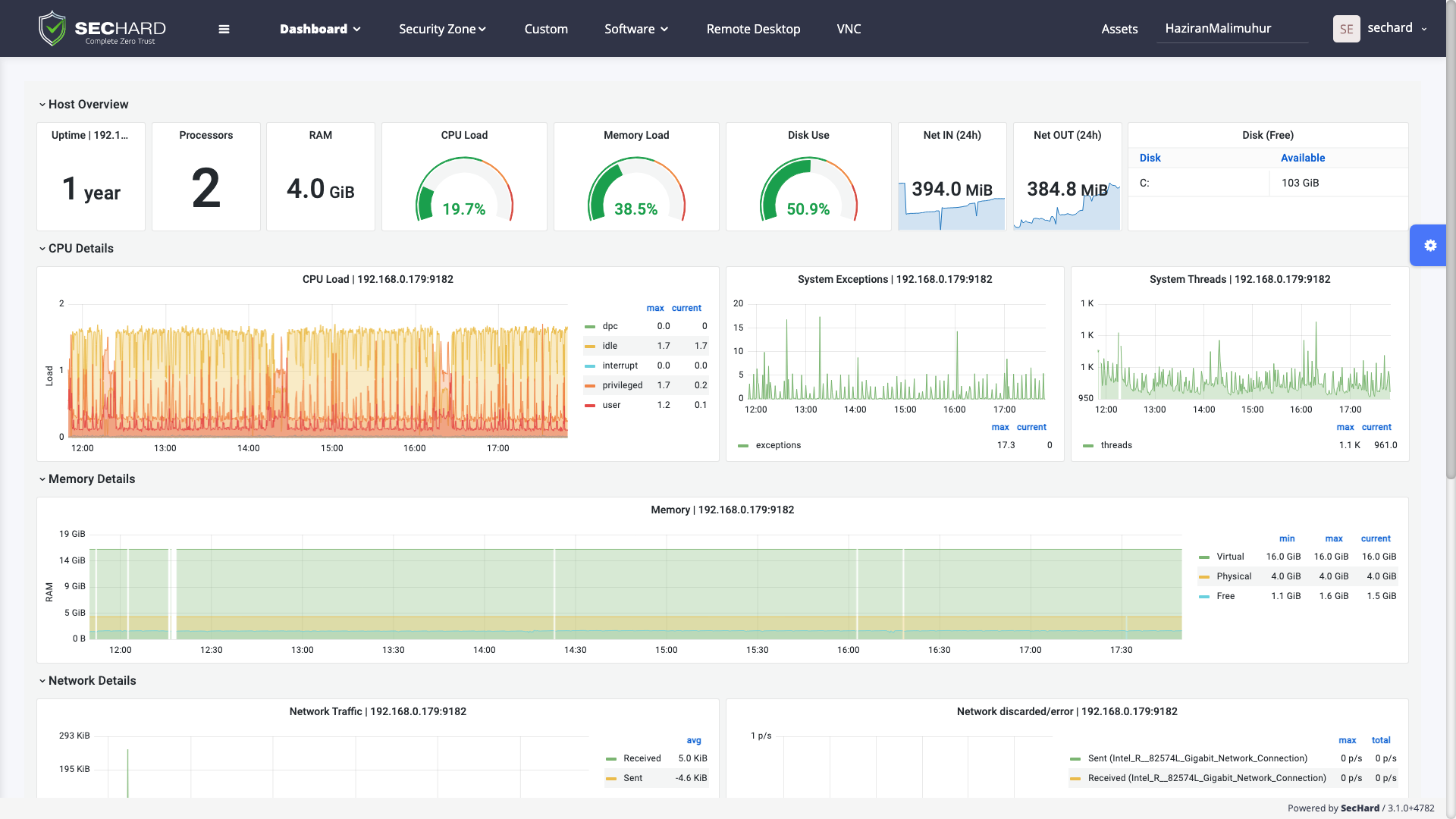
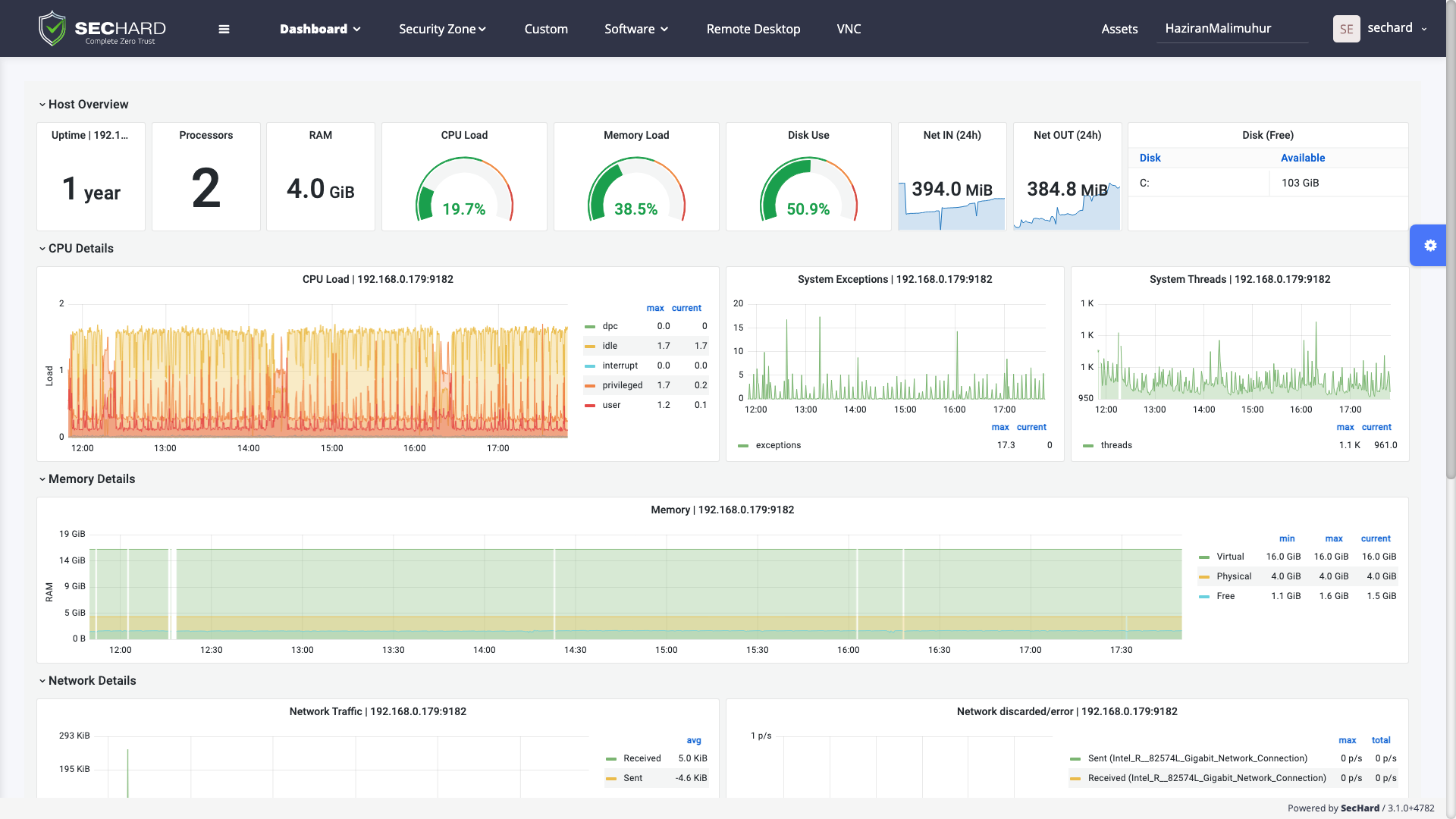
Availability is as important as privacy and integrity in the information security equation. According to the ZTA, performance and availability are two factors that should be monitored considering security controls and risk management.
SecHard provides integrated performance and availability monitoring for both servers and network devices. This integrated architecture makes it possible to monitor servers and network devices data coming through VMI, Nod, and SNMP exporters via an advanced dashboard. SecHard’s customizable dashboards show real-time information to monitoring teams.
It is impossible to monitor hundreds of assets with the human eye from screens in large networks. SecHard monitors critical assets on behalf of monitoring teams. It can generate alarms, send e-mails, and run trigger predefined actions when thresholds are exceeded. In addition, SecHard stores performance data historically and simplifies capacity planning.
The SecHard performance monitor tool provides monitoring services for all types of devices and software with IP addresses such as desktops, servers, databases, web services, SMTP services, IP cameras, network printers, routers, switches, etc.
SecHard provides automated security hardening auditing, scoring and remediation for servers, clients, network devices, applications, databases, and more.
A powerful identity and access management software to get compliant with Cyber Hygiene and to prevent attacks like privilege abuse, ransomware and more!
SecHard solves the risk awareness problem in asset management. Automated discovery, access, identify and remediation features provide ultra-wide visibility for all regulations.
With the passive scanning method, SecHard operates the vulnerability detection and management processes for all IT assets without creating any risks.
SecHard auto-discovers the certificates in companies’ environment, reports the expiration dates of these certificates, and it can automatically renew some of these certificates through well-known certificate authorities.
SecHard's unique risk assessment formula calculates the real-world risk scores by combining asset group risk scores, security hardening scores, and vulnerability scores.
Powerful and customizable network device management with backup/restore, configuration change detection, performance monitoring, bandwidth monitoring, and firmware upgrade.
Integrated performance and availability monitoring for servers, network devices, databases, applications, IoT, and industrial control systems.
Centralized Authentication, Authorization and Accounting (AAA) for *nix systems and network devices with Microsoft Active Directory integration.
Simplified log management across network devices and servers, real-time alarms based on critical events, log forwarding in Syslog and CEF formats.
Book a meeting with SecHard experts.
