Zero Trust Architecture (ZTA) is a cybersecurity framework that has gained significant attention in recent years due to its effectiveness in addressing the evolving threat landscape. Unlike traditional security models that rely on perimeter-based defenses, ZTA adopts a more proactive and comprehensive approach to protecting digital assets. At its core, ZTA operates on the principle of “never trust, always verify,” meaning that every user, device, and network component must be authenticated and authorized before being granted access to resources, regardless of location or network environment. This shift in mindset and approach aims to minimize the potential attack surface and mitigate the risk of unauthorized access or lateral movement within a network.
By implementing ZTA, organizations can significantly enhance their security posture and reduce the likelihood of successful cyberattacks. The architecture emphasizes the need for continuous verification, monitoring, and control throughout the entire network infrastructure. ZTA leverages various security technologies such as multifactor authentication, micro-segmentation, encryption, and least privilege access to ensure that only authenticated and authorized entities can access specific resources. The granular access controls and segmentation provided by ZTA limit the impact of potential breaches and restrict lateral movement within the network, even if a single component is compromised. As a result, ZTA helps organizations establish a stronger security foundation, adapt to dynamic business environments, and protect sensitive data from unauthorized access.
While ZTA offers improved security and resilience, organizations face several challenges during its implementation. In this post, we will explore organizations’ challenges when migrating to a Zero Trust Architecture.
Integration of Existing Technologies:
Implementing ZTA requires organizations to leverage the integration of various existing technologies, which may have different maturity levels and have yet to be designed to interoperate. Organizations often have a diverse technology landscape with different security solutions, network infrastructure, and access management systems. Ensuring compatibility and interoperability between these technologies can be complex and time-consuming. It may require customization, the development of connectors, or even the replacement of certain systems to establish seamless communication and data sharing between different components of the ZTA.
Lack of Time and Resources:
Organizations may need more time and resources to evaluate and determine the best combination of ZTA technologies that would work for their specific needs. Assessing different solutions, conducting proofs-of-concept, and evaluating their effectiveness can be time-consuming. Additionally, organizations must allocate resources for staff training, implementation, and ongoing management of the ZTA. The lack of dedicated personnel and budget constraints may hinder the organization’s ability to adopt ZTA effectively.
Developing Policies and Resource Prioritization:
ZTA requires organizations to identify and prioritize their resources and develop explicit policies for granting access based on specific conditions. These conditions can go beyond traditional factors such as subject identity and role and may include attributes like subject and resource location, time of day, device health status, and more. Developing and managing such policies can be daunting for organizations, as it requires a comprehensive understanding of their resources, data criticality, and the associated risk profiles. Policy development also demands continuous monitoring and updates to adapt to evolving threats and changing business requirements.
Lack of Asset Inventory and Data Understanding:
Often, organizations need a complete inventory of their assets, including hardware, software, and data repositories. With a clear understanding of what assets exist and their criticality, it becomes easier to implement ZTA effectively. Organizations must identify and categorize their assets, determine the sensitivity of their data, and understand the interactions between subjects, resources, applications, and services. This information is crucial for designing appropriate access controls and segmentation strategies within the ZTA framework.
Integration with Legacy Technologies:
Many organizations have substantial investments in legacy enterprise and cloud technologies. Migrating to a Zero Trust Architecture requires organizations to balance leveraging existing investments while gradually integrating new technologies aligned with the ZTA principles. Understanding how legacy systems fit into the ZTA framework and ensuring their compatibility with new security solutions can be complex. It may require conducting thorough assessments, making strategic decisions regarding upgrades or replacements, and addressing interoperability challenges during the integration process.
Lack of Interoperability Knowledge and Resources:
Organizations need to fully understand the potential interoperability issues involved in implementing ZTA. They may need more knowledge or resources to assess different technologies’ compatibility and identify potential conflicts or gaps. Network administrators and IT staff may require additional training and upskilling to manage and maintain the ZTA environment effectively. Organizations may also find developing a pilot or proof-of-concept implementation beneficial to identify challenges, evaluate solutions, and inform a comprehensive transition plan.
User Experience and Operational Impact:
One concern organizations have when adopting ZTA is how it may impact the operation of their environment and the end-user experience. ZTA introduces additional authentication and access controls, which could result in users needing to authenticate themselves repeatedly, depending on the resources they are accessing and the strictness of enterprise security policies. While ZTA should ideally enhance security transparently, organizations must carefully design and test their implementation to minimize disruptions and ensure a seamless user experience.
Lack of Common Understanding and Maturity Assessment:
There may be a need for common understanding across the organization regarding ZTA, its benefits, and how to gauge its ZTA maturity. Determining the most suitable ZTA approach for the business requires thoroughly assessing the organization’s security posture, risk tolerance, and business objectives. Developing an implementation plan requires collaboration between stakeholders, including IT, security, and business teams. A shared understanding of ZTA and its implications is crucial for successful adoption and implementation.
In summary, migrating to a Zero Trust Architecture presents several challenges for organizations. These challenges include integrating existing technologies, resource constraints, policy development, asset inventory, integration with legacy systems, interoperability concerns, user experience considerations, and fostering a common understanding within the organization. Addressing these challenges requires careful planning, resource allocation, collaboration between teams, and a phased approach to implementation.
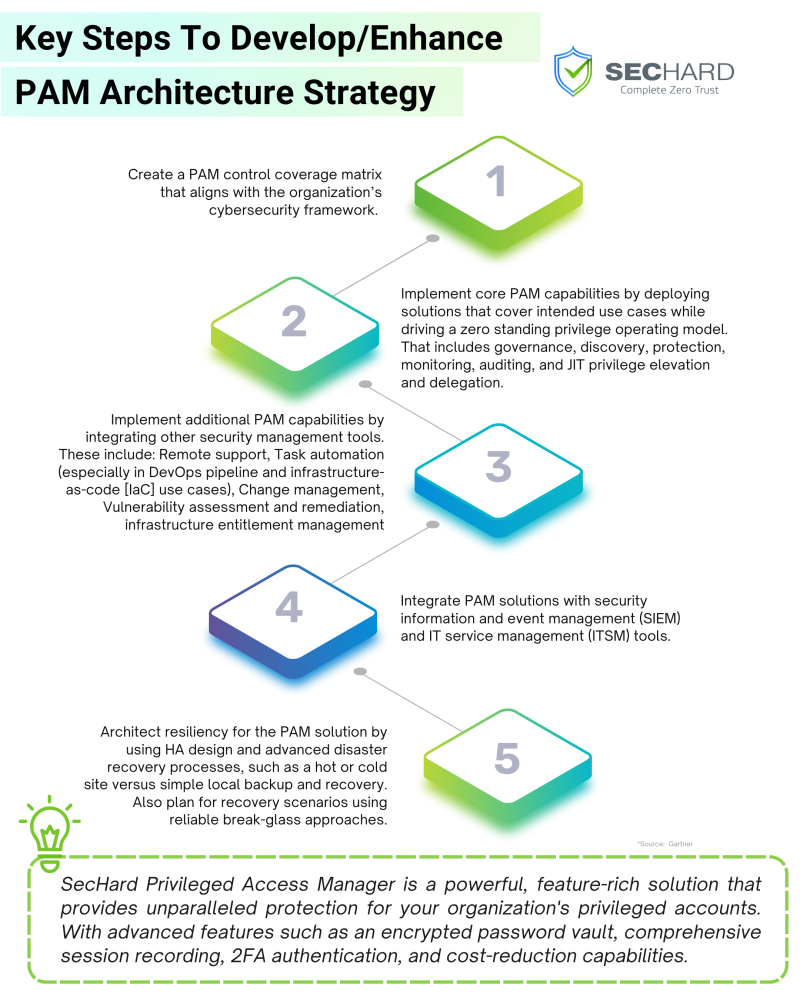
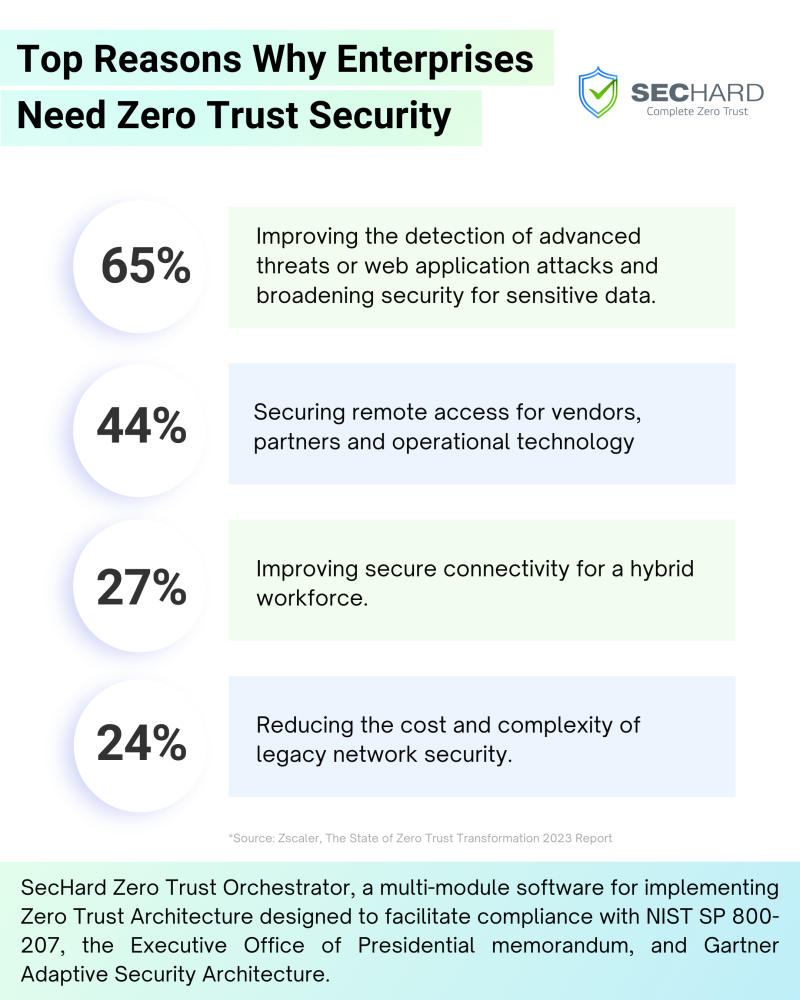
SecHard Zero Trust Orchestrator: Comprehensive Security for Zero Trust Architecture Implementation
SecHard Zero Trust Orchestrator is a robust solution designed specifically to address the challenges of implementing Zero Trust Architecture (ZTA). With a core focus on ZTA principles, it provides organizations with the necessary tools and capabilities to seamlessly fulfill the requirements set forth by the Executive Office of the President Memorandum (M-22-09) and NIST SP 800-207 Zero Trust Architecture publication.
One of the key advantages of SecHard Zero Trust Orchestrator is its ability to automate the execution of the NIST Cybersecurity Framework functions and the recommended processes outlined by the Gartner Adaptive Security Architecture. By automating these tasks, organizations can streamline their implementation process, eliminate the need for extensive expertise, and ensure compliance with industry-leading security frameworks.
SecHard Zero Trust Orchestrator enforces the core tenets of Zero Trust by treating all devices and users as untrusted entities. It thoroughly authenticates every access request, ensuring that only authorized and authenticated entities gain entry to critical resources. Adopting a comprehensive access control approach helps maintain the integrity and security of the enterprise network, minimizing the risk of unauthorized access, lateral movement, and potential breaches.
In summary, SecHard Zero Trust Orchestrator provides organizations with a comprehensive solution for implementing Zero Trust Architecture. Automating key processes, ensuring strict authentication measures, and aligning with industry standards, help organizations establish a robust security foundation and effectively mitigate the challenges associated with ZTA adoption.
Book a free demo to learn more: https://sechard.com/book-a-demo/ or contact us at [email protected].
Check out these infographic posts you might find interesting!